Passwords have become a quintessential part of our digital lives, yet they are often overlooked. They are the keys to our digital identities, unlocking access to sensitive and personal information. In this article, we'll go over the steps in creating a strong password, and more importantly, keeping it secure.
Creating a Strong Password
Crafting a strong password is more than picking random letters, numbers and symbols. Follow these creative steps to create a strong and unique password.
A longer password is generally more secure against modern day cyber threats. Follow these tips to get started:
- Start by selecting random words that could loosely form a phrase or a sentence
- Consider words related to the service or website (e.g. "money sink" for a home improvement store)
- Look at your surroundings for adjectives and nouns
- Have fun and challenge yourself to come up with a humorous or nonsensical phrase (e.g. five feet of sunshine in late December)
- Need help picking some random words? Start with this random passphrase generator
Avoid these pitfalls
- Avoid well-known phrases and idioms such as "the quick brown fox jumps over the lazy dog", "all for one and one for all", or "time flies when you're having fun". Although common phrases are easier to remember, they're also easy to guess and attack.
- Avoid cultural, personal or literary references, such as your favorite sports team, movie, significant dates, place to eat or famous quotes. Those who know you can easily guess your password, especially if you posted or tweeted about it on social media.
- Avoid being a lazy password walker
Follow along example
For our example, we picked "yellow hopscotch buckets tonight" as our initial set of words.
Use these techniques to add variety and complexity and make your new phrase unique.
- Substitute letters for numbers or symbols, and mix lowercase and uppercase.
- Misspell words intentionally, or leave out certain letters.
- Add flair by inserting random numbers or special characters.
*Side note - Although substitution does not increase resistance to brute-force attacks, it aids in creating unique passwords that protect against commonly derived passwords and reuse.
Avoid these pitfalls
- Avoid common substitutions such as replacing a 0 for an o, a 1 for an i, a $ for an S, etc. Password cracking and guessing algorithm can easily predict these behaviors.
- Although 13 is our favorite number, avoid using it in your passwords since people know you are affiliated with Colgate.
- Keep in mind any site-specific complexity requirements you may need to satisfy.
- Some websites and services may not support all special characters or blank spaces.
- Avoid reusing any examples posted on the Internet, including the ones in this article. These should be considered exposed passwords.
Advanced tip
If supported by the website or service, spice things up by adding emojis for how you feel at the moment.
Image courtesy of Webroot
Follow along example
Using some of these techniques, we've made "52Yelow hupScotch b0ckets tUnight!" our unique passphrase.
Coming up with a unique and complex password is good, but being able to remember it is even better! Here are some ideas for making your passphrase memorable.
- Visually picturing the words or phrase in your head
- Make it meaningful by associating your personal views and experiences
- Wrap the phrase with context by making a short story
- Being consistent with how you apply the 'uniqueness' techniques above means less to remember
The following time-honored comic illustrates our personal struggle with creating and remembering good passwords.
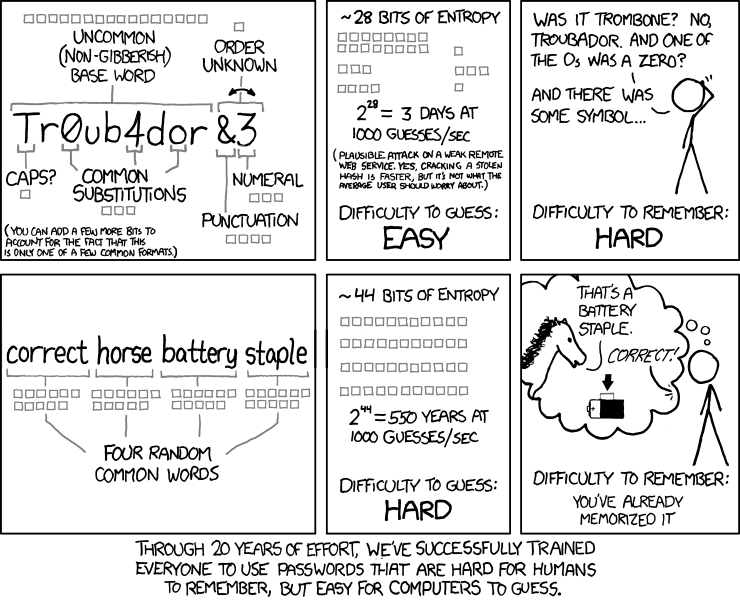
Image courtesy of XKCD
Follow along example
Here's how we can remember our new passphrase, "52Yelow hupScotch b0ckets tUnight!" with a simple story:
- There are seven (5 + 2) days in the week, and today was a nice day to walk home.
- It sure felt good with the warmth of the Yelow sun on my back.
- Along the way, I passed some kids playing hupScotch, and drumming on some old b0ckets.
- But alas, I better get home and start preparing dinner for tUnight!.
Fun fact - it would take approximately 7.052e+28 years to brute-force attack this passphase.
Keeping your Passwords Secure
Now that you've come up with a strong password, take these steps to keep it secure.
Although it may be convenient, avoid reusing the same password for different accounts or sites.
If your password was exposed due to a data breach at one website, it can be reused by attackers to log into other unrelated websites. Even though it would take 7.052e+28 years to crack "52Yelow hupScotch b0ckets tUnight!", it only takes a single misconfigured or compromised website to expose this secret.
Read more about how attackers reused passwords from an unrelated LinkedIn breach
To avoid having to share passwords, find alternative ways such as issuing a separate user account. This way, access is also tied to an individual identity.
For group or resource accounts, utilize a password manager that supports granular access control features. These settings will allow you to define allowable actions such as using the password to log in, but not being able to see what it is set to. Granular access control can also define who is authorized to change or update the password.
And remember, when updating or changing your password, don't merely increment a couple of characters in your current password. Instead, perform the steps above to create a brand new password.
When logging into a website, ensure it is protected with encryption by looking for the padlock symbol. Please note (!) that the presence of a padlock is no longer effective in determining whether a website is legitimate or part of a phishing scam.
If your password was inadvertently disclosed in a phishing attempt or sent in an unencrypted email, consider the password exposed to the world and compromised. Perform the steps above to create a new password.
Proactively monitoring your accounts will put you one step ahead of an attacker seeking to reuse your password. Check if your account and password was exposed and sign up for notifications at Have I Been Pwned
Even if your password is compromised, Two Factor Authentication (2FA) adds an additional authentication step that an attacker must somehow bypass. Enabling 2FA on your accounts and services will greatly increase the workload on the attacker.
Check here to see which websites or online services support 2FA
More Information
Ask for Help
If you are unable to find the information you need in the documentation available online, the ITS Service Desk is available to assist.