Information and guidance for Colgate students, faculty, and staff to remain secure from Phishing email attacks.
What is a Phishing Attack?
A phishing attack is a method used by criminal hackers to dupe their victims into giving up their credentials or other information in order to gain unauthorized access to their account(s) and take over their identity and/or finances.
Phishing emails are not merely annoyances like spam, they are real threats to your privacy and online security.
Of the myriad ways criminals try to steal online identities, phishing is the most common. Most phishing attacks begin with a user receiving an unsolicited email that appears to come from their company's IT department or service desk, a shipping courier, a government agency, a bank or some other financial institution, or any high-profile company with which one might do business. These emails are known as phishing emails. Phishing attacks; however, can also begin with an unsolicited phone call, text message, fax or even a flyer.
Some phishing emails are designed to trick you into clicking on a link which leads to your computer getting infected with malware - malware designed to watch your keystrokes and grab passwords or install "back doors" which hackers then use to take control of your computer. They then use your computer to hack in to systems and servers on your network and beyond. This is important to remember as even just clicking a link within a phishing email can have bad consequences.
Phishing attacks are designed to take advantage of their victims through manipulation — often through fear. The emails are made to look legitimate to make you trust the information. The subject is meant to make you feel uncomfortable, triggering you to take action to "correct" the situation.
Examples
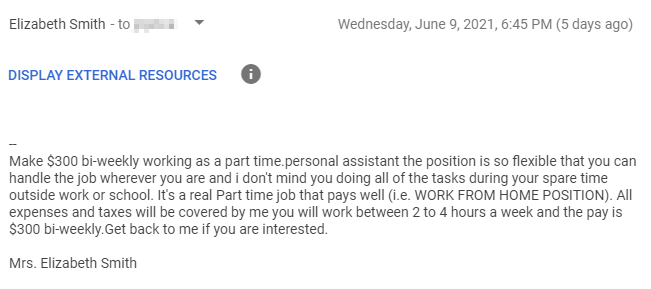
From: Prof. Michael Hardey <hardymicheal6301@gmail.com>
Date: Wed, May 25, 2021 at 9:04 AM
Subject: STUDENT EMPLOYMENT
To:
Colgate University, Department of Political Science urgently requires the services of students to fill the position of Research Assistants and get paid $300 for 6 hours weekly . The position is open to students from any department of the institution and tasks will be carried out remotely for now. Materials needed to carry out assignments will be provided by the department. Contact the department desk officer with a copy of your resume via this email or the departmental chair professor at (555) 555-1234 stating your full name, department and year of study to proceed further.
Best regards,
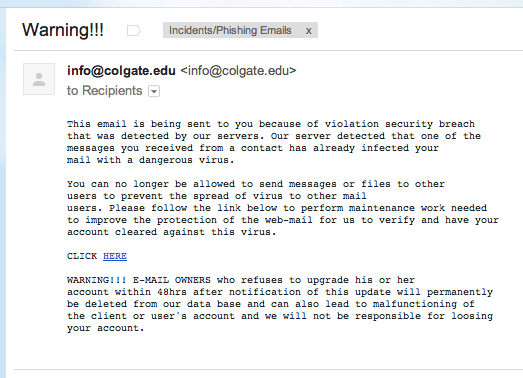
In this example, we see the classic email that looks like it comes from a service desk asking for your username and password in order to ensure your account is not turned off. This is quite common. Often, the subject line is something akin to, "Warning! Email Quota Limit" or something similar. The emails often threaten, "permanent deletion," or "infection!!!"
It is important to remember that most legitimate organizations do not email you asking you to click a link and enter your username and password in order to keep you email flowing. While some organizations do practice this type of contact with their end users, they go to great strides to use proper English and a common template. Either way, always, always be weary of links embedded in an email especially when the email is unsolicited. As you see in this email below, you can tell it is a phishing attempt by hovering your mouse over the "CLICK HERE" link. Notice (in the bottom image) how the link goes to some place other than colgate.edu?
Try it. Hover your mouse (don't click) over this link, http://www.yourbank.com. Notice what it says in the bottom-left of your browser? Creating links in an email like this is trivial to the common criminal hacker.
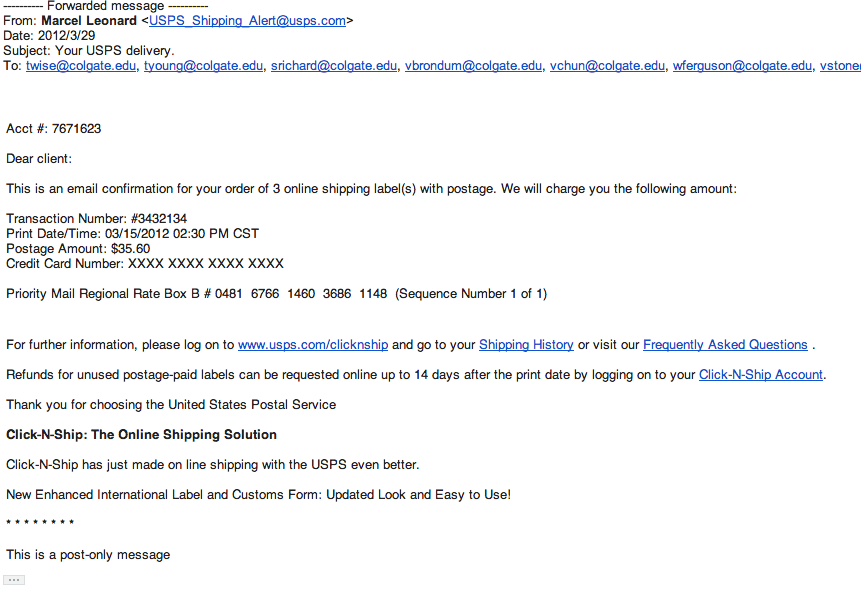
In this example, notice the email looks like it came from usps.com. The body of the message even looks like an email you might get concerning a legitimate shipping transaction.
Once again, if you were to hover over the links in the actual email, you'd notice the what the link says and where it points are not the same place destination.
How to Spot a Phishing Email
As seen in the examples above, one of the ways you can spot a phishing email is to hover over the links in the message (don't click) and see if the actual destination matches the text displayed in the body of the email. Here are more things to consider when determining if the email you received is legitimate:
- Did the email come to you unsolicited?
- Is the sender a stranger to you?
- Is the sender's email address domain different from the company's web site?
- Is the link in the email different from the organization it claims to be?
- Does the email claim to be from a service desk and talk about account "quotas"?
- Does the email claim to be from a service desk and talk about infections?
- Does the email claim to be from a law enforcement agency?
- Is the email from an online shopping site you never use or haven't used lately?
- Does the "To:" field in the email list hundreds of names and email addresses?
- Does the email sound threatening in any way, especially legally or financially?
- Does the sender of the email use poor grammar?
- Does the link go to (example) "colgate.webs.com"? (not colgate.edu)
- Does the link say, "c0lgate.com" instead of colgate.edu?
- Is the email from an individual's email address instead of an official account?
- Is it tax season?
- Is it a holiday season?
- Has there been a major tragedy in the news lately?
- Did you receive the email early in the morning or late at night (after hours)?
If you can answer yes to any one (or more) of these questions, the email may be a phishing attempt. Phishers like to use "scare" tactics as well as humanitarian needs to dupe their victims into clicking their links and providing their information. They often try hard to make the email look legit and avoid sending their emails during normal business hours.
Recognizing a Real Email Alert from ITS
ITS will send you actual alerts from time-to-time. These alerts:
- Follow a specific pattern
- Come from designated senders and accounts
- Never threaten to shut off your account
- Never send you to sites to "verify" your account credentials.
Emails from ITS will always come from one of the following accounts:
- ITSAlerts@colgate.edu
- ITSComms@colgate.edu
- ITSInfo@colgate.edu
- broadcast@colgate.edu
Protect Yourself
Protecting oneself from a phishing attack is not complicated; however, as phishing emails become more sophisticated, it becomes the potential to become a victim is greater. Here are some tips to avoid becoming a victim, steps you can take that would minimize the damage if you do, and steps you should take if you do fall victim to a phishing scam.
There are many ways to avoid becoming a victim of phishing and to prevent its propagation.
- Be skeptical and vigilant. Ask yourself the questions listed above when reading your emails.
- Turn on spam filtering. While this won't catch all phishing emails, it will catch some.
- Never click the links in any unknown, unsolicited email, ever.
- Install and use antivirus software on your computer that scans incoming emails.
- Always keep your computer, its browsers, plug-ins and antivirus up-to-date.
- Report incidents to ITS and/or the real institution portrayed in the email.
- Send phishing emails to your Spam folder by following these instructions from Google.
There are many things you can do to minimize the impact of a phishing scam should you become a victim.
- Don't use your business email for personal use.
- Never send passwords, credit card, bank account, or social security numbers in an email, ever.
- Change your passwords often and never use the same password on different accounts.
- Purge your inbox on occasion.
- Don't use email for sensitive conversations.
- Report incidents immediately.
Even if you just clicked the link and didn't give-out your credentials, you should do the following. The link may have installed malware that collects your information as you type.
- Report the incident to ITS immediately.
- Report the incident to the real institution ASAP.
- Run a virus scan on your computer (yes, even on a Mac).
- On a clean computer, change your password(s) on all your accounts.
- If your bank account may be compromised, enroll in a credit monitoring service.
- Watch for suspicious activity in all your online accounts.
Ask for Help
If you are unable to find the information you need in the documentation available online, the ITS Service Desk is available to assist.